Our smart devices tend to be too slow, or not be our preferred software. Many a times we often imagine our devices as humans, so we could hit them. Am...
The threat to our digital world cannot be emphasized. Several methods have been devised to spread awareness about cyber security to the end users. Notable references have been made in...
In our last article, we examined different kinds of hackers and ways to protect your devices. Hacking has always existed since the beginning of life itself. It was only executed...
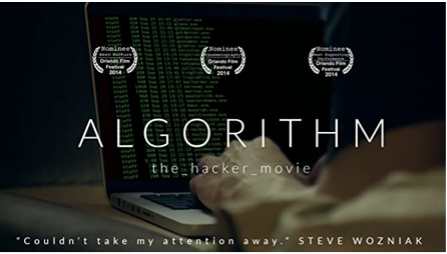
According to the Endpoint Detection and Response - Global Market Outlook (2017-2026) report, the adoption of cloud-based and on-premises EDR solutions are going to grow 26% annually and will be...
The intranet has been put in place to facilitate growth and give employees easy access to information. While we enjoy these swift services, we also need it secured for our...
It’s not new that hackers device new means of getting sensitive information from our system. But do we have good hackers? ...
There are lots of opinions about the safest way to protect your online data. Utilizing the best cloud services would protect your data in the safest way, free from malicious...
Having knowledge of cyber threats, cyber security and the cyber space in general is important for users of computer systems....
There are lots of malicious attacks happening on the internet in the word today. Cyber criminals are devising new methods of obtaining our personal information for dubious purposes. One of...
Computers and mobile devices are at risk of being violated by cyber criminals. They are devising new means of social engineering to penetrate users’ software, penetrating the system to hack...








Recent Comments